Description
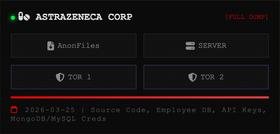
Lapsus$ is a cyber extortion group first observed in late 2021, known for high-profile breaches and data theft campaigns against major global companies rather than traditional ransomware encryption. The group primarily focuses on data exfiltration and public leak threats without encrypting victim systems. Lapsus$ uses a combination of social engineering, SIM swapping, MFA fatigue attacks, and purchasing access from insiders or access brokers to infiltrate corporate networks. Their victim list includes Microsoft, Okta, NVIDIA, Samsung, Uber, and telecom operators, with operations targeting multiple regions worldwide. Once inside, Lapsus$ actors exfiltrate source code, proprietary data, and customer information, often leaking samples to pressure victims into negotiation. The group is known for a brash and public-facing style, communicating directly with followers on Telegram channels and occasionally mocking victims. Several members, including minors, have been arrested in the UK, but the group’s activities have persisted in some form.