Description
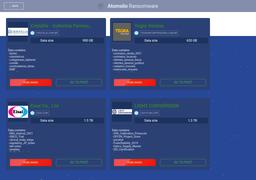
AtomSilo emerged in September 2021 and ceased operations by year-end 2021. It functioned with a double‑extortion model, combining file encryption with data exfiltration and leak threats. The malware uses a hybrid encryption scheme—AES‑256 for file encryption and RSA‑4096 to secure the AES key—and appends the extension .ATOMSILO to encrypted files. Ransom notes follow formats like README-FILE-{computer name}-{timestamp}.hta or ATOMSILO-README.hta. Structurally and operationally, AtomSilo closely resembles the LockFile ransomware and is attributed to the Chinese state-linked actor BRONZE STARLIGHT (aka Cinnamon Tempest, DEV‑0401, Emperor Dragonfly, SLIME34), likely serving as a smokescreen for espionage-driven data theft. Victims spanned multiple industries and countries, including notable high extortion demands up to $1 million USD. The group also exploited the Atlassian Confluence vulnerability (CVE‑2021‑26084) for initial access and used DLL side‑loading for stealthy deployment.